Dusting Attack for Dummies | What Is Dusting Attack?
Disclaimer: This is absolutely what you think. It is indeed financial advice, and if you follow it, take responsibility for your decision to follow it. You are a grown-up now. Don't come wailing back to me if it did not work.
I was kidding. This is not financial advice.
What Are We Discussing Today?
I wrote earlier about dusting attacks and how people can literally expose their wallets by transacting unsolicited tokens appearing in their accounts or wallets. The bad part is that you, as the owner stand to lose all your savings. So, you've got to be careful.
We will attempt to look at the dusting attack with an equivalent real-life example to simplify it. See if it helps and if it does, do let your friends and others know about such attacks. Why not keep them safe as well.

The other sadistic reason I am writing this post is to get back at another author on a particular platform who has no clue what a dusting attack is but acted too pricey to learn. I call it sadistic because I intend to derive pleasure from someone else's misery. I hope there is no misery. I hope I can let go of this sadistic part of me. I hope that author and I can be good friends in the future.
Lastly, I hope this article makes sense to most readers and my followers. 😊

Dusting Attack | Let's Take a Few Examples
The best way to start this is by looking at my wallet and finding some unsolicited tokens appearing out of nowhere.
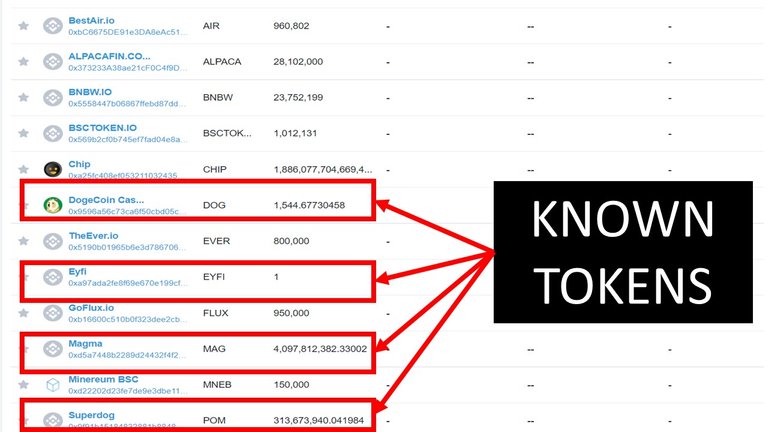
The tokens in red are the ones I bought or got from an airdrop. So, I know the sources of those tokens. The rest are the interesting ones. A few of the pointers to know that there are scam tokens in your wallet is the name. I mean, BSCTOKEN.IO is desperately begging you to visit the site. But here is the fun part. I did try to reach out to the site and see what I found.
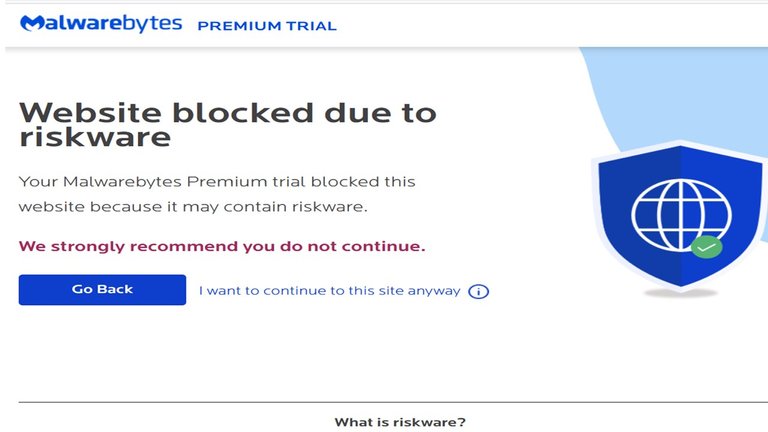
My anti-malware software blocked the site. Do you need any more proof that the site you wish to visit is going to be rigged to get information from you? I guess not. But then, all sites aren't so visibly manipulative. Some may appear docile to pass under the radar of anti-malware and anti-virus programs that you may have. The first clue they want to hack you is when they ask you to link your wallet to sell or transact those tokens. You connect your wallet, and YOU LOSE EVERYTHING FROM YOUR WALLET.
So, far it was easy to follow. But if this is what the dusting attack was all about then, you already know that. It is similar to any malware or virus attack that nefarious sites try to accomplish. True. Dusting attack, though, is more than that.

Dusting Attack Explained
You see, the dusting attack goes beyond our common understanding of virus and malware attacks. How is that? If you so much try to transact those unsolicited tokens, you would be exposing your wallet. But how? This is how. The hackers try to deanonymize your wallet by sending tokens, and when you try to transact those tokens, you leave a signature (like heat signature in aircraft) on the blockchain. These hackers use these signatures to find and hack your wallet.
Wo ho ho, hold on, man. That was too much. In English, please.
Let's say you are a thief who wants to make good from your neighborhood. But you don't know who stays in which house and what kind of people stay there. You come up with a novel idea. You buy a few dollars worth of gifts from Amazon and have them delivered to each of the addresses in the neighborhood. Remember, getting the address is not as tricky as finding who stays in the address. You also leave a note giving your name and a contact number and adding that the receiver can get more gifts or money by calling you back. Voila! You got the ball rolling.
Now, all those who got the gift will comprise people who don't care and never call back. These are equivalent to crypto users who would not transact unsolicited tokens. But then, this small group (or maybe big) will call back, and that's when you derive more information about a particular address. Those people who call back are like the ones who end up transacting the tokens to earn more. As a thief, based on the calls, now you know which address has how many people, their details, etc. You then plan the robbery. There is a good chance you will get away with it. This is the modus operandi of the dust attack hackers too.
The minute you transact the tokens, you give away additional information about your wallet. The hackers will find you and take away all you have in your wallet (or virtual home). That's what a dusting attack is all about.

So, What Should We Do?
Nothing. And that's precisely what you do.
Never try to move the tokens to another wallet. Never try to transact (sell, etc.) and never ever go back to the site (if specified) to link your wallet. There are dusting attacks where the hacker leaves information asking you to go back to their site or pay a certain amount of BNB to sell the tokens. Clearly, that's not what you do. 😊
Do dusting attacks take place in all chains? Bitcoin, BSC, ETH, etc.?

Dusting Attack | The Usual Chains Where It Happens
Understand that the hacker is not here to do charity but to hack your wallets. But if the cost of hacking is way too high, they will not want to go ahead. In our above example, if Amazon says that the delivery charges for the thief's packages (gifts) are ten times the gift's cost, the thief would lose interest. It is just too costly. What does that mean for a dusting attack?
It means, if the fees on the chain are too high, it wouldn't be lucrative for a hacker to send tokens on those chain to thousands of addresses. So, Bitcoin and ETH are, therefore, relatively safer. That would mean the newer chains like BSC, TRX, and others are at high risk of being played by hackers. One way to check this is to go to your ETH, BSC, TRX, HECO, or other wallets and check where you see more unsolicited tokens. I bet it would be the low-fee chains like BSC, TRX, and the kind.
Am I right. Of course, I am. 😊
So dusting attack is a terrible thing, then? Not always.

Dusting Attack | Good or Bad
Let's take two examples to see conditions where dusting attacks did happen, but it is for a good cause (supposedly).
1. WSG Tokens
I had written about the WSG tokens earlier. WSG tokens appeared in my wallet all of a sudden from nowhere. Initially, I thought it was a dust attack, and I still do. But on closer examination, the site now seems to be operational and the token listed on the MEXC exchange. It may be on other exchanges as well.
The part that baffles me is why someone would send tokens if they are legitimate? Well, it could be it was one way of getting users to come to the site to play the games over there. The tokens were like a starting gift or an airdrop, if you will. WSG stands for Wall Street Games.
I am still a bit cautious of the tokens in my wallet and will never touch them. Though, I will go on MEXC and buy more tokens and even trade. I wouldn't move those tokens to my wallet from the exchange, though. See, my point. I will wait for a couple of years to ensure these guys are legitimate.
2. Governments and Agencies Involved in Dusting Attack
This is by far the newer version of known dusting attacks. The issue here is that tracking accounts and users in a decentralized environment are complex for governments across the globe. They have no clue if you are playing in crypto unless you let them know on your own. Or the laws of your land make it illegal to trade in crypto without letting your government or tax authorities know.
Even then, there would be those who wouldn't come ahead voluntarily. So, what do the governments do? Dusting attack. It is a new occurrence that has come to the fore. If you don't want your government to run behind you with dust attacks, let them know of your holdings.
And if you are smart, you would know not to transact those tokens that appeared out of nowhere.

Can Dusting Attack Happen Through Known Tokens Too? | Possibly, Yes
If the known tokens are cheaper and can be sent as dust to wallets and exchanges, it still can be a dusting attack. Binance had found the same some years back and taken measures to curb such dust attacks. Is the world safer, therefore? Possibly, yes, but that would never convince me to use unsolicited tokens.
So, be careful of tokens appearing out of nowhere. Don't run to make money out of such tokens and stay safe from hacking. I hope this gives a perspective to dusting attacks and will help you stay safe from such attacks.

Image Courtesy: Ijmaki @Pixabay
Some Useful Sites to Give You More
Some of the good crypto-writing-earning sites:
Publish0x: Earn ETH || Read.cash: Earn BCH || Trodl
Some good earning sites for Tweet size posts
Torum: Earn XTM || Noise.cash: Earn BCH || Tipestry: Earn Dogecoin, Dogecoincash & SuperDog
Some crypto-faucets and jewelry earners:
Horizen: Earn ZEN || Mene: Earn $5 on signup || Earn Litecoin || Earn Bitcoin || Pipeflare: Earn ZEC, FLR, MATIC
Few Gaming-cum-earning sites
Splinterlands || Drugwars ||
Spot and/or Futures Trading Exchange
Binance || KuCoin || WazirX || Bityard